Security Key Support for Apple
The giant will introduce support for utilizing physical Security Keys to secure your Apple ID and iCloud accounts better. There’s also a new function for iMessage, dubbed iMessage Contact Key Verification by the business.
About this security initiative
First and foremost, Apple has stated that beginning in 2023, customers will be able to improve the security of their Apple ID and iCloud accounts by utilizing hardware Security Keys. This means you’ll have an actual hardware device that you may configure to function as your account’s second tier of two-factor authentication.
Apple’s Security Key mechanism is integrated with its device-to-device transfer method. So as long as you follow the device-to-device setup transfer method when setting up a new iPhone, you won’t have to verify your iPhone with the Security Key again.
Furthermore, Apple claims that trusted devices that are already signed in to your Apple ID will not be signed out when you use the Security Key function to authenticate. Instead, the inclusion of a Security Key is intended to prevent sophisticated attacks in which hackers try to log in to your Apple ID on an unknown, untrusted device.
“This takes our two-factor authentication even further, preventing even an advanced attacker from obtaining a user’s second factor in a phishing scam,” Apple adds.
Apple will not provide a hardware Security Key. Instead, it will rely on third-party services. In addition, the firm is collaborating with the FIDO Alliance to achieve cross-platform interoperability with open standards.
See Rhyno Cybersecurity in Action
iMessage Contact Key Verification
Second, Apple is introducing a new iMessage security feature. This feature, known as iMessage Contact Key Verification, enables iMessage users to “further verify that they are messaging only with the people they intend,” Apple states.
The feature works by notifying users who have activated the precaution if an unusually sophisticated bad actor, such as a state-sponsored attacker, were ever to succeed in compromising cloud servers and inserting their device to eavesdrop on these encrypted conversations.
The Contact Key Verification function must be activated for users chatting over iMessage. Users using iMessage Contact Key Verification may compare a Contact Verification Code in person, over FaceTime, or in another secure conversation for additional protection. This verification code is available via the Messages app.
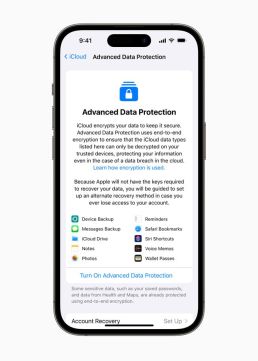
The picture above depicts what the “Advanced Data Protection” screen looks like. As part of this feature, when an unknown device is added to the other person’s account, you’ll get in-line information in your Messages thread stating that “an unknown device may have been added” to that person’s account.
What are Hardware Security Keys?
Hardware security keys are physical devices that are used to provide an extra layer of security for online accounts. They are often used with a username and password to provide two-factor authentication, which helps to protect against unauthorized access to an account.

Hardware security keys typically take the form of small USB devices plugged into a computer or mobile device. When a user attempts to log in to an account requiring a hardware security key, they must insert the key into their device and press a button to confirm their identity. This additional step helps ensure that only the account’s legitimate owner can access it.
Some of the benefits of using hardware security keys include the following:
- Improved security: As mentioned, hardware security keys add an extra layer of protection to your online accounts, making it much harder for attackers to access your sensitive information, even if they have your password.
- Convenience: Many hardware security keys are minor and easy to carry so you can use them on the go. Some even support multiple accounts so you can use the same key for your online accounts.
- Easy to use: Most hardware security keys are easy to use and require little to no setup. Plug the key into your computer and follow the on-screen instructions to log in to your account.
Overall, a hardware security key can provide an extra layer of security for your online accounts without sacrificing convenience or ease of use.
In my humble opinion
Apple consistently emphasizes that these capabilities are intended for consumers who have the potential to suffer concerted threats to their online accounts. This covers persons such as celebrities, journalists, and government officials. According to Apple, most customers will never be targeted by such sophisticated cyberattacks.
With that in mind, Apple agrees that certain functionalities are required for consumers who are explicitly looking for them. Apple says the company is unaware of any iCloud server breaches but is continually battling against threats.
For most users, two-factor authentication is enough security for their Apple ID and iCloud accounts. According to Apple, two-factor authentication is utilized by 95% of active iCloud accounts, making it the most frequently used two-factor account security method in the world.
Security Keys for Apple ID will be available internationally in early 2023, while iMessage Contact Key Verification will be available later that year.
Cheers!
Dan Duran, CTO @ rhyno.io
Sharing is Caring!
You are welcome to put this blog article on your website, provided you also append an active link to our website “Source: https://resources.rhyno.io”
For media enquiries, contact us at [email protected].
MANAGED CYBERSECURITY SOLUTIONS
Rhyno delivers a range of activities that combine to fully protect your infrastructure and data from cybercriminals, anywhere and everywhere, 24/7/365.
About Rhyno Cybersecurity Services
Rhyno Cybersecurity is a Canadian-based company focusing on 24/7 Managed Detection and Response, Penetration Testing, Enterprise Cloud, and Cybersecurity Solutions for small and midsize businesses.
Our products and services are robust, innovative, and cost-effective. Underpinned by our 24x7x365 Security Operations Centre (SOC), our experts ensure you have access to cybersecurity expertise when you need it the most.