Recent investigations have brought to light a series of sophisticated attacks posing a significant threat to the forward secrecy and future secrecy guarantees of Bluetooth Classic. These exploits specifically create scenarios for adversary-in-the-middle (AitM) attacks between already connected peer devices.
[FREE E-BOOK] The Definite Blueprint for Cybersecurity in Manufacturing
The vulnerabilities extend across Bluetooth Core Specification versions 4.2 through 5.4, collectively identified as BLUFFS. These issues were responsibly disclosed in October 2022 and are cataloged under CVE-2023-24023, carrying a CVSS score of 6.8.
As detailed in a recent paper by Daniele Antonioli, a researcher at EURECOM, the attacks facilitate device impersonation and machine-in-the-middle scenarios across sessions with the compromise of just one session key. This exploit, disclosed at the end of the previous month, exploits two newly discovered vulnerabilities in the Bluetooth standard’s session key derivation technique.
These vulnerabilities enable the generation of the same key across multiple sessions, amplifying the risk associated with the compromise of a single session key.
In key-agreement cryptographic protocols, the concept of forward secrecy plays a crucial role in preventing the disclosure of previous communications. Even if a passive attacker exposes the private keys related to a specific exchange, forward secrecy ensures that past interactions remain confidential.
Conversely, future secrecy, sometimes referred to as backward secrecy, guarantees the confidentiality of forthcoming messages in case the keys employed in previous exchanges are compromised.
To put it simply, forward secrecy acts as a protective measure for past sessions, safeguarding them from potential compromises of keys in the future.
The execution of this attack involves exploiting four architectural weaknesses within the Bluetooth session setup process specification. These vulnerabilities encompass the two previously mentioned gaps. The primary objective of the attack is to use these weaknesses to generate a vulnerable session key, susceptible to brute-force attacks, ultimately allowing the attacker to impersonate individual victims.
Following the generation of the weak session key, the Adversary-in-the-Middle (AitM) attacker can initiate a connection with the other end, establishing subsequent encryption operations using legacy encryption. This deceptive maneuver involves impersonating the paired device to deceive the target.
“An attacker in proximity may ensure that the same encryption key is used for every session while in proximity and impose the lowest permitted encryption key length,” The Bluetooth Special Interest Group (SIG) has highlighted. “This is because the attacker is able to ensure that the same encryption key is used.”
“Any conforming BR/EDR implementation is expected to be vulnerable to this attack on session key establishment. However, the impact may be limited by refusing access to host resources from a downgraded session or by ensuring sufficient key entropy to make session key reuse of limited utility to an attacker.”
Moreover, an adversary can exploit these vulnerabilities to perform real-time brute-force attacks on the encryption key, allowing for live injection attacks on traffic between susceptible peers. The feasibility of this exploit is rooted in the fact that the encryption key is not encrypted.
For the attack to succeed, the adversary must be within the wireless range of two vulnerable Bluetooth devices engaged in a pairing procedure. Additionally, the attacker needs the capability to capture Bluetooth packets in both plaintext and ciphertext, including the victim’s Bluetooth address, and possess the ability to craft Bluetooth packets.
The SIG recommends Bluetooth implementations to reject service-level connections on an encrypted baseband link with key strengths below 7 octets. Furthermore, they advocate for devices to operate in “Secure Connections Only Mode” to uphold adequate key strength, emphasizing the preference for pairing to be conducted in “Secure Connections” mode rather than the legacy mode.
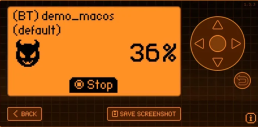
This advisory coincided with ThreatLocker disclosing a Bluetooth impersonation attack capable of exploiting the pairing mechanism. This attack has the potential to gain wireless access to Apple macOS systems through the Bluetooth connection, allowing the execution of a reverse shell.
MANAGED CYBERSECURITY SOLUTIONS
Rhyno delivers a range of activities that combine to fully protect your infrastructure and data from cybercriminals, anywhere and everywhere, 24/7/365.
About Rhyno Cybersecurity Services
Rhyno Cybersecurity is a Canadian-based company focusing on 24/7 Managed Detection and Response, Penetration Testing, Enterprise Cloud, and Cybersecurity Solutions for small and midsize businesses.
Our products and services are robust, innovative, and cost-effective. Underpinned by our 24x7x365 Security Operations Centre (SOC), our experts ensure you have access to cybersecurity expertise when you need it the most.